I know we all don’t have a lot of time to read and digest the information. I have put this
document together to help skip to the good stuff. I’ve added a few tips of my own with the
browsers that I’ve used. If you want all the information, please consider reading the entire
article found at https://restoreprivacy.com/secure-browser/
The article above recommends the Tor browser. However, there is mounting evidence that the Tor browser has been compromised and is no longer trustworthy. See Tor Browser below for more information.
You can test your current browser for WebRTC leaks and browser Fingerprinting by visiting
https://crypto.blacklab.net/test/
Recommended Browsers
Brave
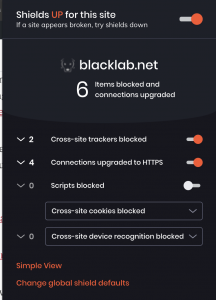
Brave is a Chromium-based browser that is fast, secure, and privacy-focused by default with a built-in ad blocker. The main developer behind Brave is Brandon Eich, who formally worked for Mozilla. For out-of-the-box privacy and security, Brave is a decent option.
Brave is based on Chromium, with many privacy-abusing features/preferences stripped out. Brave does well with its default privacy settings and extra features. Here is a brief overview:
- Blocks ads and trackers by default
- Protects against browser fingerprinting
- Built-in script blocker
- Automatically upgrades to HTTPS (HTTPS Everywhere)
WebRTC – It’s also worth noting that all Chromium-based browsers are vulnerable to the WebRTC leak issue, whereby your real IP address can be exposed, even if you are using a VPN service. While there are solutions to WebRTC leaks for all browsers, but with Chromium, you’ll need to block WebRTC because it cannot be completely disabled (such as with Firefox).
Keep in mind, however, that to effectively “block all fingerprinting” you will probably need to consider other factors as well – see the browser fingerprinting guide. You can read more about Brave’s privacy and security features here: https://brave.com/features/
Did you think your identity was safe while using a VPN? Nope, you’re not. Reading through the 2 articles below will help you understand how to keep your identity from being leaked out without you knowing it.
What is a WebRTC leak? https://restoreprivacy.com/webrtc-leaks/
What is Browser Fingerprinting: https://restoreprivacy.com/browser-fingerprinting/
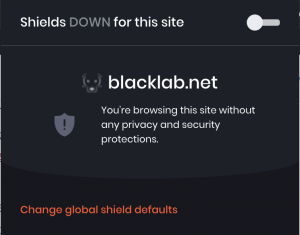
One quick tip on using Brave. Some sites break when you leave the Shields Up option that Brave leaves on by default. A quick shields down will fix the issue.
How to configure your Brave browser to protect and secure. https://www.techrepublic.com/article/how-to-protect-and-secure-your-web-browsing-with-the-brave-browser/
Firefox
Firefox is a great all-around browser for privacy and security. It offers strong privacy protection features, customization options, excellent security, and regular updates with an active development team. The newest version of Firefox, Firefox Quantum, is fast and light-weight with many customization options.
Out of the box, Firefox is not the best for privacy, but it can be customized and hardened, as explained in my Firefox privacy modifications guide https://restoreprivacy.com/firefox-privacy/. Be sure to disable telemetry in Firefox, which is a feature that will collect “technical and interaction data” and also “install and run studies” within your browser.
NOT Recommended Browsers
Tor
Most people think Tor is the ultimate for online anonymity. I hate to break the news to you, but that’s not the case anymore. Here’s why.
According to Roger Dingledine (Tor co-founder) and other key Tor developers, getting people (outside the US government) to widely adopt Tor is very important for the US government’s ability to use Tor for its own purposes. In this goal, they have largely succeeded with Tor being widely promoted in various privacy circles.
Here are some surprising truths about Tor.
Tor is compromised and not anonymous. Governments can de-anonymize Tor users is another well-known fact that Tor promoters are ignoring.
Washington Post Article – https://www.washingtonpost.com/world/national-security/secret-nsa-documents-show-campaign-against-tor-encrypted-network/2013/10/04/610f08b6-2d05-11e3-8ade-a1f23cda135e_story.html
“Since 2006, according to a 49-page research paper titled simply “Tor,” the agency has worked on several methods that, if successful, would allow the NSA to uncloak anonymous traffic on a “wide scale” — effectively by watching communications as they enter and exit the Tor system, rather than trying to follow them inside. One type of attack, for example, would identify users by minute differences in the clock times on their computers.”
Washington Post
Tor developers are cooperating with US government agencies. Some Tor users may be surprised to know the extent to which Tor developers are working directly with US government agencies. The journalist, Yasha Levine, was able to clarify this cooperation through FOIA requests, which revealed many interesting exchanges. There was an email correspondence in which Roger Dingledine discusses cooperation with the DOJ (Department of Justice) and FBI (Federal Bureau of Investigation), while also referencing “backdoors” being installed.
No warrants are necessary to spy on Tor users.
“The U.S. Federal Bureau of Investigation (FBI) can still spy on users who use the Tor browser to remain anonymous on the web. Senior U.S. District Court Judge Henry Coke Morgan, Jr. has ruled that the FBI does not need a warrant to hack into a U.S. citizen’s computer system. The ruling by the district judge relates to FBI sting called. Operation Pacifier, which targeted a child pornography site called PlayPen on the Dark web. The accused used Tor to access these websites. The federal agency, with the help of hacking tools on computers in Greece, Denmark, Chile and the U.S., was able to catch 1,500 pedophiles during the operation.”
Tor was created by the US government for a reason. Roger Dingledine, co-founder of Tor in a 2004 speech.
“I forgot to mention earlier, probably something that will make you look at me in a new light. I contract for the United States Government to build anonymity technology for them and deploy it. They don’t think of it as anonymity technology, though we use that term. They think of it as security technology. They need these technologies so that they can research people they’re interested in, so that they can have anonymous tip lines, so that they can buy things from people without other countries figuring out what they are buying, how much they are buying and where it is going, that sort of thing.”
Roger Dingledine
Tor is funded by the US government. Financial data showed that Tor wasn’t the indie-grassroots anti-state org that it claimed to be. It was a military contractor. It even had its own official military contractor reference number from the government.
- US Agency for Global Media (spun off from CIA) – $6.1 million
- State Department – $3.3 million
- The Pentagon – $2.2 million (2011 through 2013)
Safari
Safari is the default browser for Mac OS and iOS devices. Overall, Safari is not a horrible choice in terms of privacy and tracking protection – but it also cannot be recommended for a few reasons:
Apple is a partner in the NSA PRISM program: https://en.wikipedia.org/wiki/PRISM_(surveillance_program)
Apple was caught “hoarding” Safari browsing history – even after it was deleted https://www.forbes.com/sites/thomasbrewster/2017/02/09/apple-safari-web-history-deleted-stored-icloud/#2c6980f26328
Apple was found to be collecting Safari history even when used in private mode. https://www.fastcompany.com/3044018/safari-private-browsing-history-is-not-forgotten-after-all
On a positive note, however, Apple does somewhat better with privacy than other large companies. The Safari browser blocks third-party cookies by default and also implements cross-site tracking protection.
Google Chrome
When it has the name Google in it, you know it has to be gathering everything it can get its greedy little hands on. But if you run into issues with other browsers, it’s a good backup to see if it’s a browser issue or a site issue.
Google Chrome is a secure browser, but it also collects quite a bit of data. While it remains the most popular browser on the market, Chrome is not the best choice for privacy.
Microsoft Internet Explorer/Edge
Edge is a Microsoft product. Just like with Windows, it’s a good idea to avoid Microsoft products, including Internet Explorer, and their newer browser, Edge. Internet Explorer and Edge are also closed-source, so there’s no telling what’s going on behind the scenes, and they’re also not the best for privacy reasons.
Opera Browser
Opera started off as a decent browser, developed in Norway. However, in 2016 it was sold to a Chinese consortium for $600 million – and a lot has changed. Opera’s privacy policy explains how your data is being collected and shared when you use Opera products.
Epic Browser
Epic is a browser based on Chromium, created by “Hidden Reflex” which is based in India. Since 2014, Epic has been claiming they would open source the code, but it remains closed source today. What’s going on behind the scenes? How do they manage Chromium and remove invasive code? Who knows.
Just like with Opera, Epic falsely claims to offer a “free VPN” through the browser, but this is not really true. The browser is merely routing traffic through a US proxy server. As we learned with Opera (and with many other “free proxy” services), proxies are frequently used for data collection (and they are often not secure). Sure enough, when reading the privacy policy, data from “video download and proxy services” is being collected.
One person who analyzed Epic found it to be connecting to Google on startup. This means that Epic is not, in fact, de-googled as it claims.